Stop chasing the latest .env.
Keep secrets and setup docs in one local vault.
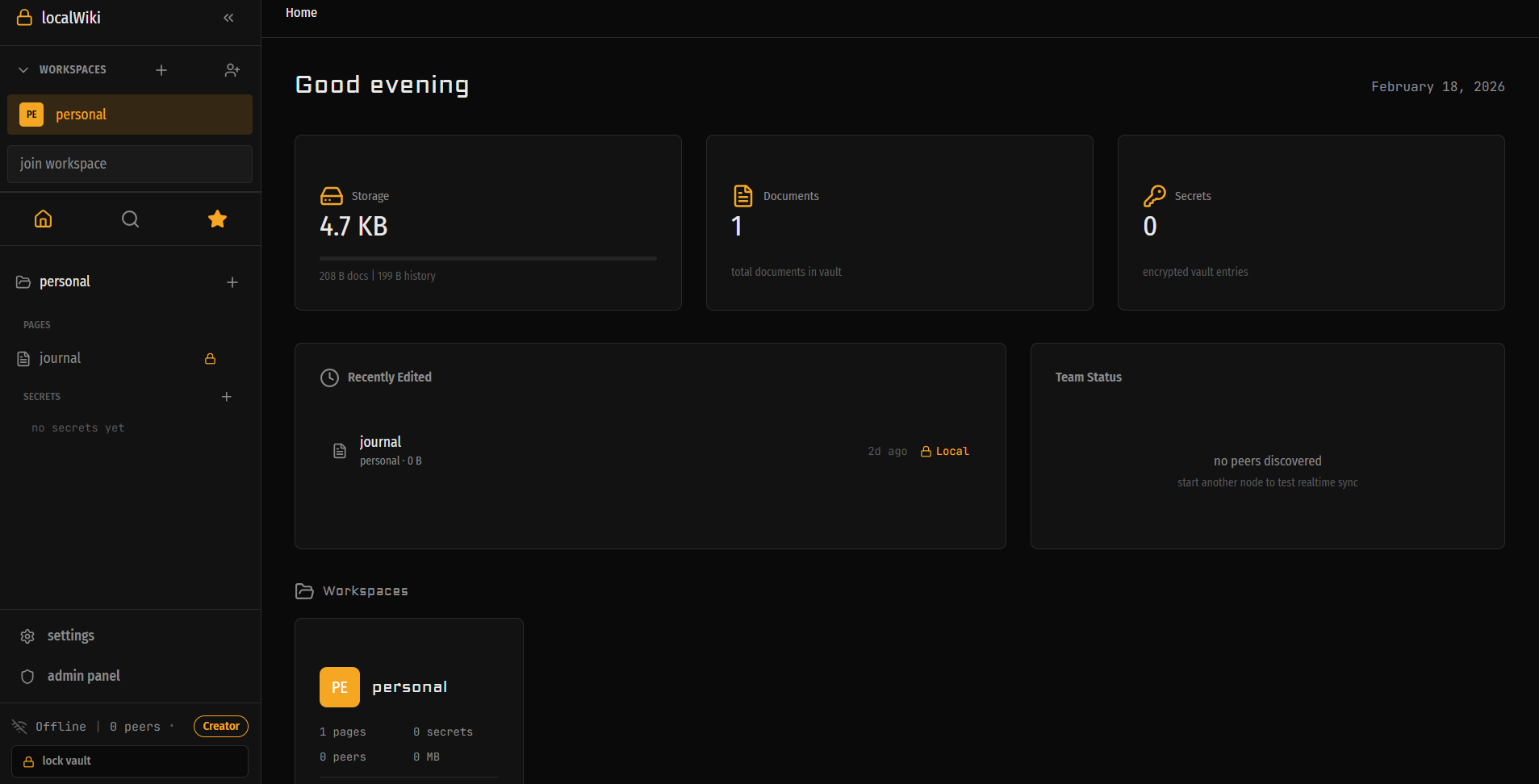
localWiki gives teams one encrypted place for canonical secrets, environment notes, onboarding runbooks, and audit history, so you stop pasting keys into chat apps, wikis, and temporary paste tools.
Approved-device sync. Audit trail. No cloud copy of your vault.
Your secrets process is probably held together by memory and paste links.
Small teams rarely mean to build secret sprawl. It just happens: Chat threads, wiki pages, temp paste tools, and one person who “knows the right values.”
The API key changed. Half the team still has the old value in a chat thread or a forgotten note.
A new developer needs five setup steps, three secrets, and two tribal-knowledge caveats before the app even boots.
When staging breaks, nobody trusts which doc matches the current environment anymore.
localWiki gives your team one canonical place for secrets and the setup docs around them.
Rotate a secret once, keep the runbook next to it, sync it to approved devices, and stop asking who still has the right keys.
Built for the boring, expensive work every team keeps repeating.
localWiki is not trying to be your company wiki. It is for the secrets, setup docs, and environment history that decide whether a project boots cleanly or wastes the team’s morning.
Canonical secret rotation
Update the real API key, DB URL, or staging credential once. Keep one source of truth instead of six conflicting copies.
Setup docs next to the env values
Store the runbook with the secret: where it is used, which service depends on it, what to restart, and what changed.
Faster new-dev onboarding
Approve a device, sync the shared vault, and give the new dev the actual setup context instead of sending them on a chat-thread scavenger hunt.
Rotate a secret once. Sync the right environment to the right team.
This is the core commercial use case: one person updates the real value, localWiki keeps the setup context with it, and the rest of the team gets the correct version without another chat thread.
Update the canonical secret
Rotate an API key, webhook secret, or staging DB URL in one place instead of chasing stale copies.
Keep the runbook next to it
Add the setup notes: which app uses it, which environment it belongs to, what to restart, and why it changed.
Sync it to approved devices
Teammates pair their devices, receive the updated vault, and stop guessing which environment block is current.
Track what happened
Audit history shows who revealed or copied a secret, and version history lets you recover context when rotation gets messy.
billing-api / staging
canonical environment block
API_SECRET_KEY=••••••••••••••••••••
WEBHOOK_SECRET=••••••••••••••••••••
DATABASE_URL=••••••••••••••••••••
runbook
Restart the billing worker, run the webhook smoke test, and confirm payouts sync within five minutes. Update support if the old API key was exposed.
The local-first vault for secrets first, setup docs second.
Canonical secrets, not stray notes
Treat env values like production assets, not throwaway text.
Keep one named secret, one current value, and one place your team trusts.
Reveal or copy when needed without turning chat threads into your vault.
Setup docs attached to the secret
Store the runbook with the credential it explains.
Capture which app uses it, what environment it belongs to, and what changed.
Docs stay supporting cast. The secret is still the primary object.
Approved-device sync
Teammates pair devices, get approved, and receive the shared vault.
No cloud workspace is holding the team copy for you.
Relay is optional transport, not custody.
Audit trail and recovery
Track who revealed or copied a secret and when.
Use history to recover docs and context after a rushed rotation.
This is the boring reliability layer that stops small mistakes from compounding.
Keep the vault on your machines. Keep the cloud out of custody.
localWiki is for teams that want the speed of a local desktop app, the discipline of a secrets tool, and the honesty of software that does not pretend to own your environment for you.
The trust story is simple: encrypted local vault, approved-device sync, no cloud copy as the default source of truth.
What we can prove
We are not selling enterprise theater. We are selling a safer, cleaner way for small dev teams to keep secrets and setup context together without handing custody to another cloud tool.
Try it for free.
No account. No credit card. Download the app and start using it today.
Download FreePricing tiers coming soon
The questions buyers ask before they trust another secrets tool.
Is localWiki a wiki or a secrets manager?
Secrets manager first. The docs are there because developer teams need the setup context, runbooks, and environment notes next to the secret they are using.
What happens when a secret changes?
Update the canonical secret, keep the runbook notes with it, sync the new version to approved devices, and use the audit trail to see who revealed or copied what.
How do teammates get access?
Teammates join with approved devices. On the Team plan, the buyer gets teammate activation keys and can track seat redemption inside the app.
Does localWiki keep a cloud copy of our vault?
No by default. The product is local-first. Shared state syncs between approved devices, and relay is transport only, not your source of truth.